The Agentic Product Security Platform
Code-to-cloud-to-runtime integrations

30+ security scanners integrations

Internal policies + compliance reqs



Automatically triage, validate, and remediate top risks in your backlog
Learn more
Provide immediate feedback for developers on the security of every code change
Learn more
Automatically build threat models for you apps that update with every release

Generate customized, continuously updated dashboards that monitor the risks you care about most
Learn more
Sera handles AppSec noise by finding the real risks in your backlog
Rather than weeding out false positives, let our Security Evaluation and Remeidation Agent (Sera):
Learn More
Learn More
Learn More
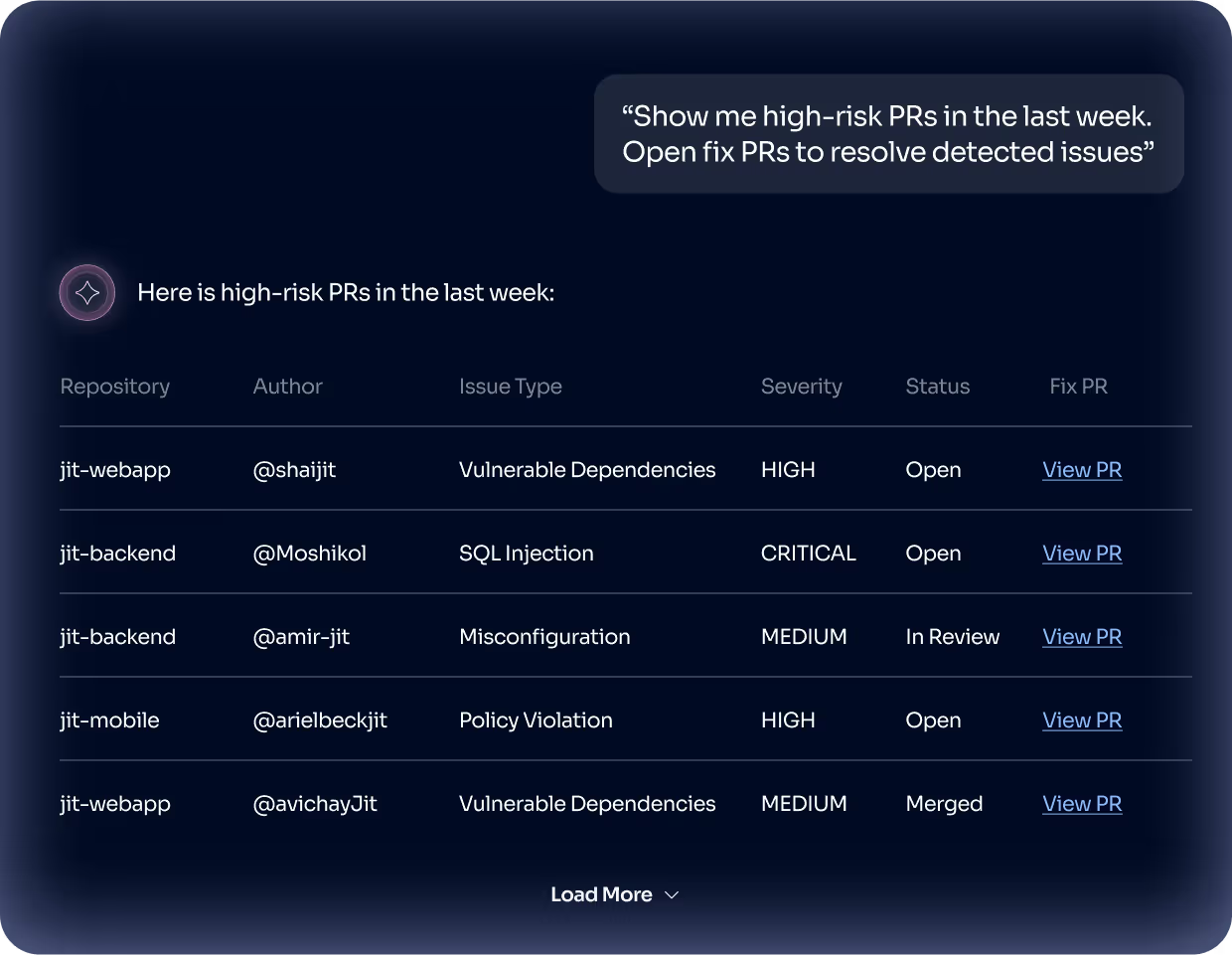
Custom, continuous monitoring with Custom AI Agents
Instead of repeatedly pulling data and creating reports, let Jit’s Custom AI Agents:
Learn More
Learn More
Learn More
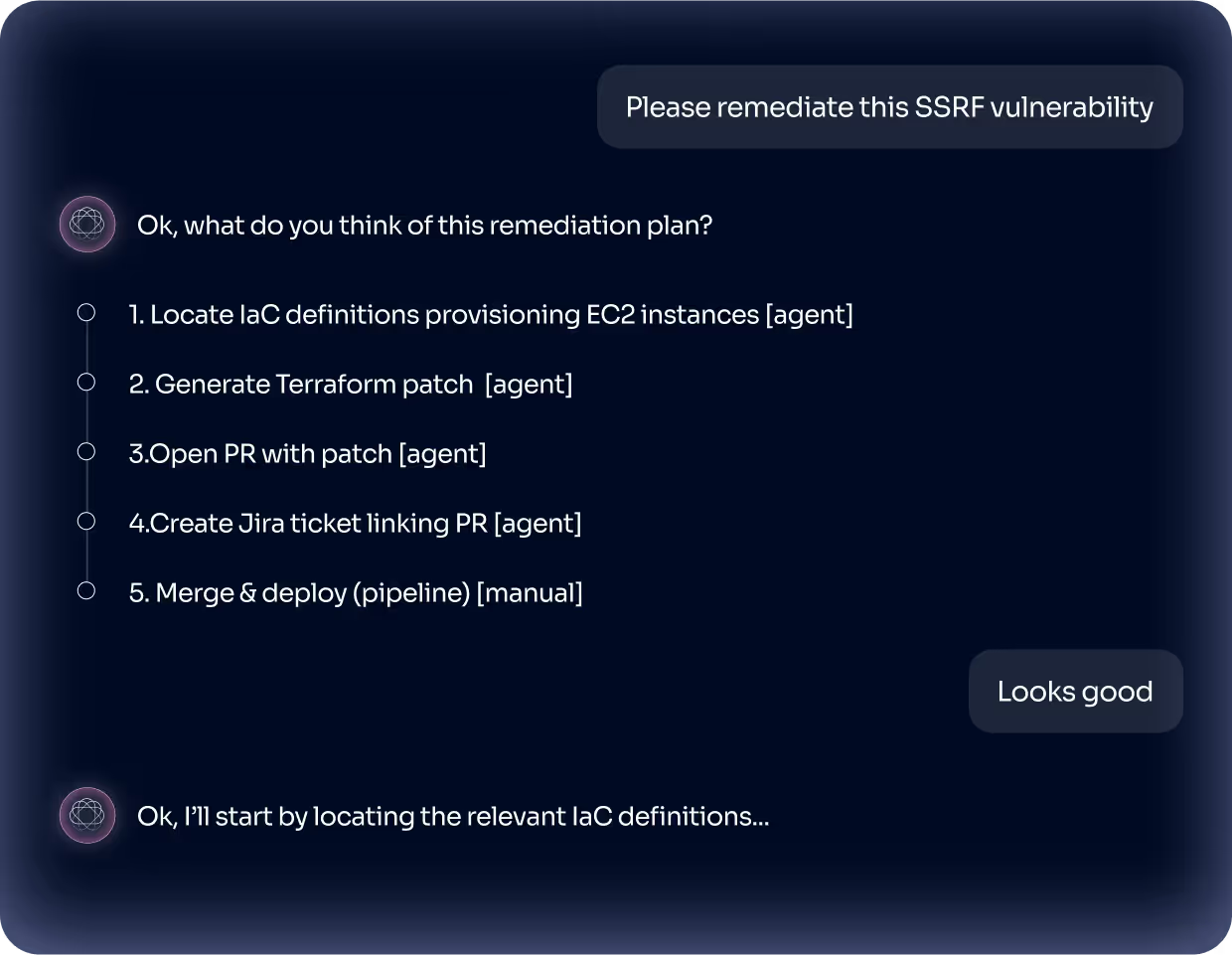
Automate remediation with Sera, while staying in the loop
Instead of clicking across tools to remediate issues, let our Security Evaluation and Remediation Agent (Sera):
Deva simplifies the developer UX for security
Instead of asking developers to manually investigate security scanner findings, let our Developer Enablement and Verification Agent (Deva):
Learn More
Learn More
Learn More
Wide security and integration coverage

What do developers
think about security?
We surveyed 150 developers to better understand what they need to deliver more secure code.

