Kubescape & Jit
Updated November 5, 2024

AI Summary
Kubescape is an open source, CNCF sandbox, end-to-end Kubernetes security tool designed to assess the security posture of Kubernetes clusters created by ARMO. It helps identify security risks and misconfigurations that could potentially be exploited by attackers, and provides automatic assistance to remediate them.
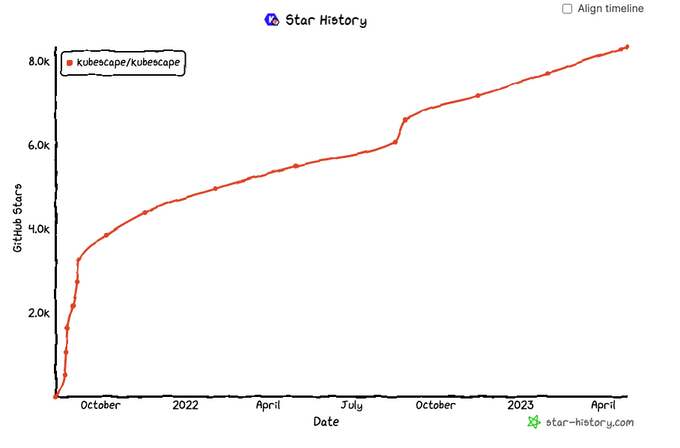
Kubescape was launched less than two years ago, in August 2021, and already has more than 8.3K stars on Github, and over 100 open source contributors. It is considered a best of breed security tool for modern Kubernetes and cloud native environments.
Kubescape is used for static and runtime scanning. It scans Kubernetes resources, including pods, nodes, API servers, services, deployments, and configuration files, to identify potential security vulnerabilities.As a result of its support for the most popular compliance frameworks and standards, including the CIS Kubernetes Benchmark, NIST, and MITRE ATT&CK, it has gained rapid adoption.
Kubescape can be used in various stages of the software development lifecycle, including: development, testing, and production. It can help ensure that Kubernetes clusters are secure from vulnerabilities and compliant with industry standards and RBAC requirements, reducing the risk of security breaches and protecting sensitive data.
With the widespread adoption of Kubernetes, this was a platform that the Jit team was seeing greater demand for supporting as an out of the box control. Therefore, we decided to roll up our sleeves and do the work to benchmark Kubescape, and test how it performs vs. other popular open source and commercial tools available today for Kubernetes security and integrate it to Jit, based on its performance.
One of Kubescape’s greatest strengths is its native compatibility in the CNCF developer and operations workflow. Written in Go, with its controls in Rego, and supporting other CNCF projects natively such as Open Policy Agent, ArgoCD, Helm and others, it is also very well-suited to integrate with typical developer and DevOps tool chains.
Kubescape helps you maintain Kubernetes security best practices and catch security issues like insecure APIs, overprivileged containers, misconfigured resources, and more. By identifying and mitigating these issues as early as possible, you can reduce the likelihood of your workloads being compromised. You will save time that would otherwise be spent resolving issues in a production environment.
We had high expectations for Kubescape to deliver on its promise.
The Jit Research Under the Hood
The Jit team benchmarked Kubescape for its static scanning of configuration files. It was compared with other popular Kubernetes security open source and commercial tools with a mix of benign repos and deliberately vulnerable ones, such as:
These were used to assess its detection quality in terms of True Positives and False Positives and compare these findings to those of other (more costly) tools. In addition, the team manually reviewed every finding and determined whether it is actually exploitable or not, where the leading determination is that findings which are not exploitable are considered noise.
Kubescape performed HANDS-DOWN better than other widely adopted Kubernetes open-source security tooling, and left the commercial competitors in the dust. 🤯 It found significantly more true positives - double the next best OSS tool (e.g. 45 in Kube Security Lab with the next competitor turning up a mere 20!).
All this with 100% accuracy, after being checked and double-checked by a security analyst. The commercial tool found a fraction of the vulnerabilities with just 7 identified. The same was true for the additional two research targets (Kubernetes goat and goof, respectively). This is practically unheard of - a 100% accuracy rate after scanning more than 25K lines of code.
This created an immediate high level of trust in the tool, as it simply excelled at detection. Kubescape provides not only more frameworks and security controls than the other tools, but also impeccable accuracy.
The next question we needed to answer - was how optimized is it for developers?
With support for both JSON and YAML configuration files, developer-friendly vulnerability names, excellent documentation, and practical remediation assistance - we found that Kubescape is highly aligned with developer workflows and processes, and thinks about security much in the same way that the Jit team does. JIt provides the added benefit of scanning the code introduced in PRs, presenting alerts inside the PR and suggesting fixes. With this integration it is now much easier to catch security risks before they are deployed to production code, and auto-fixes are coming soon too.
It is developer friendly, with minimal noise and maximum coverage. All of the things we are looking for in excellent open source tooling.
Why Kubescape?
Kubernetes is becoming the nearly de facto way for modern cloud native engineering organizations to build microservices architecture. With its growing popularity it is becoming a more popular attack vector for malicious actors. That is why Kubernetes security is becoming a mission critical aspect in system engineering.
All in all, Kubescape performed by orders of magnitude better than all the other tooling explored. Its extremely high accuracy rate is the reason it earned its best of breed status so rapidly. This tool is highly recommended for anyone using Kubernetes. It provides the peace of mind that their security tooling is catching the most up-to-date and exploitable vulnerabilities, without disturbing developers and operations engineers with noise. When integrated with Jit, Kubescape will scan the entire code base and every newly created PR, keeping developers in their own native environment.