Top 10 Cloud Security Tools for 2026
Updated August 19, 2025

AI Summary
In the rapidly evolving digital landscape, cloud computing has become an indispensable technology for developers and businesses. With its flexibility, scalability, and cost-efficiency, the cloud offers unprecedented opportunities for innovation and growth.
However, as organizations increasingly rely on the cloud to store and process sensitive data, ensuring robust security measures becomes paramount. In 2022, IBM reported that 45% of the breaches were cloud-based.
As a result, Cloud security tools have become an increasingly crucial part of the defensive posture for protecting Cloud data and applications. These tools encompass various technologies, methodologies, and practices designed to mitigate risks and protect against threats like unauthorized access, data breaches, and service interruptions. They provide DevSecOps and businesses with the means to fortify their cloud infrastructure, monitor activity, detect anomalies, and respond swiftly to potential security incidents.
Here are the top Cloud Security Tools for 2026.
Why is cloud security important?
As organizations expand and adapt to the cloud, they often need help maintaining visibility over such a complex and interconnected infrastructure. Misconfigurations are common issues that expose businesses to threats and may lead to expensive, potentially irreversible data breaches. Plus, ensuring regulatory compliance can be challenging.
Cloud providers operate under a Shared Responsibility Model, meaning that security is a joint effort between them and their customers. By leveraging cloud security tools, organizations can establish a robust security posture and ensure continuous protection of their cloud-based assets.
These tools enable proactive monitoring, rapid threat detection, and timely incident response, aligning with the principles of continuous security. As your tech stack grows, Jit automates selecting, implementing, configuring, and managing your Application Security toolchain to make continuous security simple and achievable.
Categories of cloud security solutions
Cloud security solutions can be broadly divided into the below categories. It’s important to note that it's possible for a tool to fall into multiple categories:
- Cloud Security Posture Management (CSPM)
- Cloud Access Security Brokers (CASB)
- Static Application Security Testing (SAST)
- Cloud Infrastructure Entitlement Management (CIEM)
- Cloud Workflow Protection Platforms (CWPP)
- Secure Access Service Edge (SASE).
10 Top Cloud Security Tools for 2026
Cloud Security Posture Management (CSPM)
CSPM solutions help organizations assess, manage, and remediate risks in their cloud infrastructure. They continuously monitor all their cloud applications and data to determine their risk from misconfigurations and prevent serious security issues such as data loss. With CSPM, organizations can be more proactive regarding cloud security and ensure regulatory compliance.
1. Prowler
Prowler is an open-source cloud security tool for AWS, Azure, and GCP. It enables users to conduct security assessments by analyzing its current security practices and auditing them against crucial security standards such as the CIS Amazon benchmarks, PCI DSS, GDPR, and ISO27001. Jit integrates Prowler as part of its comprehensive security plan.
Best for Cloud-native companies looking for a complete security assessment tool.
“ProwlerPro has been able to secure all of our applications across all of our cloud accounts, and as we adopt new services, we have more confidence in our security posture.”
2. Kubescape
Kubescape is an open-source tool designed to help Kubernetes users with a thorough security assessment. Despite being relatively new, it already has over 100 contributors, and it is one of the fastest-growing solutions for Kubernetes security.
With Jit, you can integrate it easily into your current CI/CD pipeline and automate the scan of your Kubernetes containerized applications in runtime to detect non-compliant configurations. Kubescape also provides real-time remediation advice.
Best for Kubernetes users.
"Kubescape is one of the most popular Kubernetes security compliance tools for developers. Its easy-to-use interface, flexible output formats, and automated scanning capabilities have made Kubescape one of the fastest-growing Kubernetes tools. This has saved Kubernetes admins and users precious time, effort, and resources."
Static Application Security Testing (SAST)
SAST tools are white-box testing solutions that analyze the entire application source code, bytecode, and binary code. They provide in-depth visibility early in the development and immediate feedback when issues are discovered, enabling faster remediation. Developers can use SAST tools to address security vulnerabilities before deploying applications to production environments.
3. KICS
KICS is an open-source Infrastructure as Code (IaC) security tool that supports multiple platforms and is extensible. It makes it easier for DevOps teams to find security and compliance issues and misconfigurations in their cloud infrastructure. It is also one of Jit's supported suite of security tools.
Best for cloud-native companies with complex environments.
"KICS (Keeping Infrastructure as Code Secure) is a free, open-source solution for static code analysis of IaC. It’s like magic."
4. SpectralOps
SpectralOps is a code security tool that helps organizations find and fix security vulnerabilities. It detects and prevents secrets leakage in software development pipelines in real-time and offers continuous integration support that works with both cloud-based and traditional applications.
Best for development teams that want to improve the security of their code and security practices.
"You can tell Spectral was built by developers for developers, and more importantly, you can see the value of using it immediately."
Cloud Access Security Brokers (CASB)
CASB solutions can be on-prem or cloud-based and enforce compliance with security policies for cloud users and service providers. They act as an intermediary between the two, giving organizations more visibility into their security posture and finding potential security gaps and risks to address.
5. Cisco Cloudlock
Cisco Cloudlock monitors your cloud infrastructure across SaaS, PaaS, and IaaS to identify and mitigate risks like data loss, malware attacks, and shadow IT. Its features include policy automation and behavior analytics to detect unusual activity.
Best for large enterprises with complex cloud environments.
"Cisco Cloudlock allows us to see the owner, what alert it triggered, and see if the owner has done anything about the notification they received...Very helpful in monitoring this type of information we don't want on the cloud."
6. Forcepoint
Forcepoint helps organizations protect their data in the cloud by providing visibility into cloud usage, preventing data loss, and controlling access to cloud apps. Moreover, it offers over 190 pre-defined policies and controls to ensure policy and regulatory compliance.
Best for businesses of all sizes that use cloud applications.
“Forcepoint NextGen firewall is one of the best firewall solutions to protect your organization network from external attacks. It also helps to optimize network uses.”
Cloud Infrastructure Entitlement Management (CIEM)
CIEM solutions help organizations manage and enforce least privilege access policies across their cloud infrastructure. These tools provide visibility into user access and permissions, enabling businesses to identify and remediate excessive permissions that could lead to security risks.
7. Skyhawk
Skyhawk Security helps organizations protect their entire cloud from cyberattacks. The company's flagship product, the Skyhawk Synthesis Security Platform, uses machine learning and artificial intelligence to detect and respond to threats in real-time. Its main features include a runtime hub for improved and real-time visibility over attack sequences, alerts only for actual attacks and not false positives, and automated remediation.
Best for organizations of all sizes that use cloud-based applications and data.
“Easy integration between CWP and AWS accounts, integration with external IDP, integration with Slack, able to send alerts to multiple channels.”
8. Zscaler
Zscaler is a scalable cloud-native security platform with zero trust access, policy enforcement, and continuous monitoring. It helps organizations protect their data and applications from cyberattacks by providing a secure way to access them.
Best for cloud-based businesses of all sizes that need a scalable and secure CIEM security solution.
"The Zero Trust Exchange helps you reduce business risk while enabling you to realize the promise of digital transformation.”
Cloud Workloads Protection Platforms (CWPP)
Cloud workloads are applications, services, or work requiring cloud resources. They have different requirements than traditional IT systems, so CWPP solutions are designed to protect them. They work for all public, private, or hybrid environments, and some of their security capabilities include vulnerability management, container security, and runtime application protection.
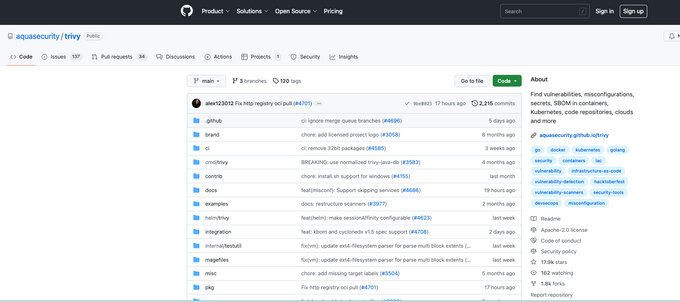
9. Trivy
Trivy by Aqua Security is an open-source vulnerability and misconfiguration container scanner for DevOps and security teams. It enables enterprises to gain improved visibility into their packages and access detailed information about vulnerabilities in real time, including their severity level and affected software. You can integrate it into your existing CI/CD pipeline and manage it easily through Jit.
Best for companies using container environments.
“I found this tool very useful as we use Kubernetes in almost all of our projects in a production environment. Using its security tool, we can be assured of our project's insight into the cloud and cluster management.”
Secure Access Service Edge (SASE)
SASE solutions combine cloud-native security capabilities like CASB, FWaaS, Zero Trust, and wide area networking (WAN) capabilities. As traditional network technologies don’t offer enough protection for digitally-driven organizations, SASE tools combine the best of both worlds to help streamline security and reduce complexity.
10. Cato Networks
Cato Networks provides a single, integrated solution for networking and security by connecting all of the cloud assets, branches, data centers, and people. It also secures and optimizes traffic in the cloud, regardless of location, and supports businesses across more than 75 global PoPs (Points of Presence).
Best for large organizations that need unified security.
"Cato can easily connect multiple sites and allow communication as one network while having one pane of glass to manage it."
Securing your Cloud for the Future
It’s easy to let security slide in today's fast-paced tech world. Employing comprehensive solutions can help you manage cloud security risks effectively and without headaches.
With Jit's orchestration layer, integrating essential tools like Prowler, Kubescape and KICS is even simpler, providing real-time alerts and remediation in a unified platform.
Start your journey towards a more secure cloud infrastructure by booking a demo with Jit.