4 Key Techniques Every DevSecOps Professional Needs (+ Core Principles)
Security practices are essential in every DevOps team, but it doesn't have to be overly complicated. There are several techniques and principles that can help you get the job done.
Updated December 31, 2024

AI Summary
DevSecOps—short for development, security, and operations—is an extension of DevOps and applies security practices throughout the software development lifecycle (SDLC) to deliver more secure code faster.
To take their career forward in this fascinating field and ship secure software on time to end users, there are a few principles that DevSecOps experts need to understand and some key techniques to help them excel.
» Take a look at the best open source product security tools
4 Key Techniques Every DevSecOps Pro Needs at a Glance
- Strong communication and teamwork skills
- Knowledge of security tools, languages, and infrastructure services
- An all-in-one security platform
- Risk assessment and threat modeling techniques
Fundamental Principles of Efficient DevOps Culture
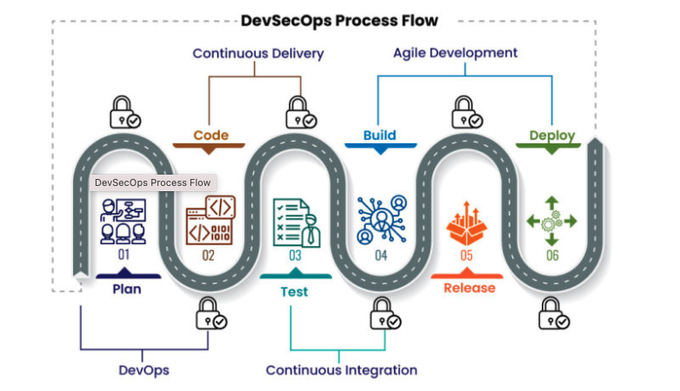
To successfully implement a DevSecOps culture, people must be well-informed about its core principles. This development practice has six fundamental principles that are a sound basis for delivering software securely:
- Deliver frequent releases with agile methodologies
- Make use of automated testing whenever possible
- Empower programmers to influence security modifications
- Ensure constant compliance
- Be prepared for security threats
- Keep investing in advanced training for the company’s engineers
The 4 Pillars of the DevSecOp Culture
- Communication Engineering organizations used to be siloed, which made it difficult for security and development teams to communicate. It's now understood that strong communication, from the executive level to ICs doing the work, is the backbone of successful DevOps.
- Collaboration In addition to building, testing, and deploying code, software developers work closely with operations teams and security experts to enhance security throughout the development phase. Everyone shares responsibility for a product's security and quality.
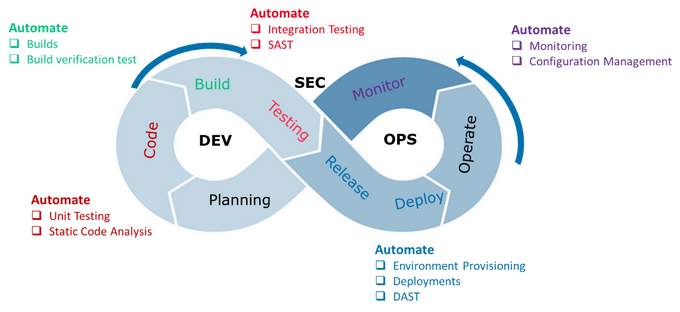
- Process By moving security from the end of the SDLC to an integral part of each person's work, software teams perform automated security evaluations, security-centric unit testing, extensive monitoring, and defensive coding to check for security breaks and speed up feedback loops.
- Technology Software teams leverage technology for automated security testing at the time of development, while DevSecOps teams use it to examine the application for security flaws without impacting delivery times.
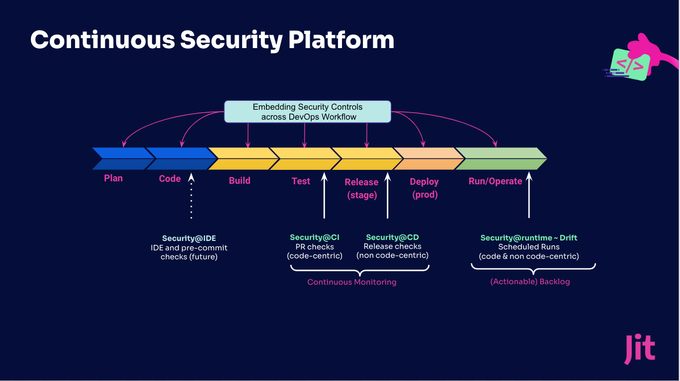
This shift-left security approach requires a technology toolkit that supports all kinds of tests throughout all phases of the CI/CD pipeline. Managing them can quickly become a problem, especially as engineers are not security experts and have other responsibilities.
Continuous Security Monitoring platforms like Jit can integrate all the security tools and controls into a single interface, automating them and making security monitoring easier for everyone.
4 Key Techniques Every DevSecOps Professional Needs
1. Strong Communication and Teamwork Skills
Effective communication and teamwork can be the difference between success and failure in a DevSecOps environment. These engineers must be able to express ideas and share knowledge of threats with their peers and employers. Collaboration tools are vital to ensuring that your team is always aligned.
DevSecOps interacts with cross-functional teams instead of being a siloed department, so everybody will need to be more involved in and familiar with business processes, product development, and support.
2. Up-To-Date Knowledge of Security Tools, Languages, and Infrastructure Services
Like DevOps teams, DevSecOps teams need to be as fast and efficient as possible. For instance, firms use various application security testing (AST) tools, which are essential to ensure the written code comes with minimal risk and to prevent malicious packages from being introduced.
These applications can be static (SAST), dynamic (DAST), and interactive (IAST). DevSecOps professionals must have a good, up-to-date understanding of AST tools, manual security, and penetration testing.
Development, the dev part of DevSecOps, is a significant part of an engineer’s everyday work. To develop customized tools for security purposes, a DevSecOps person needs a comprehensive understanding of popular and newer programming languages.
On top of this, proficiency with modern development workflows and processes, such as Git (and its modern tooling—Github, Gitlab, Bitbucket), is critical, as is integrating tools into the DevSecOps toolchain to ensure coding best practices through the CI/CD pipeline.
From the Ops perspective (at the tail of DevSecOps), this also requires a solid working knowledge of today’s popular cloud-native and infrastructure services—this can be anything from AWS, Azure, and GCP to containers Docker and Kubernetes. Note that the tooling is changing all the time as new tools are introduced and business needs shift—so continuous learning is required.
3. An All-In-One Security Platform
We have named various security tools, workflow tools, and infrastructure services in the last section. Integrating and managing these tools can get overwhelming, especially if developers lack security expertise and frequently change tools and strategies.
While it is fundamental to have high-level knowledge of each tool you are using, engineers shouldn’t be expected to master a completely different area. And they don’t have to, either. Instead, consider leveraging a tool like Jit to handle all your security stress within your workflows.
4. Risk Assessment and Threat Modeling Techniques
DevSecOps is responsible for including security practices in the application development process, identifying security threats, and configuring the network infrastructure.
Professionals in this area should have up-to-the-minute details about risks and risk assessment frameworks to implement risk assessment techniques and best security practices that match new attack trends.
Besides, all cyber security professionals must understand threat modeling methods, which includes being able to look at a security system and finding not only existing vulnerabilities but also other ways in which it can get exploited in the future.
Start DevSecOps at Full Power
Cyberattacks are going anywhere, making DevSecOps the unavoidable future of software development. A DevSecOps expert needs to understand DevOps processes, secure SDLC practices, cloud infrastructure, and application security.
Most importantly, they must know how to work together and take the initiative. With this, they can extend information security across a small team of security professionals and alleviate threats or attacks that make it to the end user. If you’re interested in seeing how Jit can help your team, you can start for free.